Much like the recent rise of the gig economy, generative AI, and air fryers, we’re in a watershed moment in privacy compliance.
Lots of states have enforced new data privacy regulations in 2023. Google is sunsetting third-party tracking in 2024. And Millennials are finally realizing reusing the same password they’ve had since middle school may not be a good idea.
There’s a fundamental shift occurring in how we deal with the security of our data — and businesses like yours are right in the middle of it.
But not every business has the luxury of a legal team to ensure users' personal data stays under lock and key.
That’s where contract management comes in.
Businesses have a responsibility to protect their customers' data, and contract management is the security guard that decides what goes in, what goes out, and who gets access.
TL;DR
- Regulations like the GDPR, CCPA, and HIPAA exist to keep sensitive data safe and secure.
- Contract management software like ContractSafe does the heavy lifting for you to ensure privacy compliance when handling contracts with sensitive information (which is probably all of them).
- CLM software can identify at-risk contracts, control who can access them, and show evidence of compliance with contract reporting.
What Is Privacy Compliance?

Privacy compliance refers to following laws and rules about keeping personal information secure. This personal information ranges from customers' names and addresses to things like warranties and legacy data.
Most U.S. states have laws in place that businesses have to follow to keep customers' information safe. Violate these regulations and you’re in for a world of heavy fines and legal trouble — not to mention damage to your company’s reputation and loss of trust in your organization.
With phishing attacks, identity theft, and other security breaches on the rise, countries are implementing extensive high-profile regulations — such as the European Union’s General Data Protection Regulation (GDPR), the California Consumer Privacy Act (CCPA), and the Health Insurance Portability and Accountability Act (HIPAA) — to ensure consumers know exactly who has access to their personal information and what it’s being used for.
Governments — and even companies — are shifting the framework governing data privacy. Here are some of the most noteworthy below:
| Privacy Policy | What It Does |
| General Data Protection Regulation (GDPR) | Standardizes data privacy laws across the EU and limits what companies can do with personal data |
| Health Insurance Portability and Accountability Act (HIPAA) | Protects sensitive patient health information from being shared or disclosed without the patient’s knowledge or consent |
| California Consumer Privacy Act (CCPA) | Gives California residents more control over the personal data businesses collect |
| Children’s Online Privacy Protection Act (COPPA) | Protects the personal information and online privacy of those age 12 and younger |
| Controlling the Assault of Non-Solicited Pornography and Marketing Act (CAN-SPAM) | Establishes the requirements for commercial emails and electronic mail messages and gives recipients the right to opt out or unsubscribe |
| Gramm-Leach-Bliley Act (GLBA) | Requires financial institutions to disclose their data-sharing practices and safeguard private customer information |
| Apple App-Tracking Transparency Feature | Allows consumers to choose whether an app can track their activity across other apps and websites for the purpose of advertising or sharing with data brokers |
| Safari Third-Party Cookie Blocking | Blocks all third-party cookies, preventing advertisers or websites from using cookies for cross-site resources |
GDPR
The GDPR is, to put it simply, the gold standard data privacy act. It was put into effect in 2018 to protect European citizens and their private data.
It applies not just to businesses actually based in the EU, but all companies that do business or collect data there, too. That means even United States businesses that sell to EU customers need to comply.
The GDPR laid out the framework for how European countries handle and protect personal information, including regulations regarding:
- Data protection: To ensure companies are transparent, accurate, and secure when processing data, and limit the amount of information that should be collected and how long it should be stored.
- Accountability: Data controllers need to demonstrate compliance by ensuring responsibilities are appropriately delegated, detailed data documentation is maintained, technical and organizational security measures are implemented, and data processing contracts are in place.
- Data security: Companies are required to implement a data processing agreement (DPA) between a data controller and data processor, in addition to other security measures like requiring staff to use two-factor authentication on personal and company accounts, implementing a company data privacy policy, or limiting access to personal data to only those who need it.
EU consumers also gained more say in how their private information is used and accessed. For example:
- A company must have evidence of consent before processing personal data.
- Consumers have the right to access, rectify, or remove sensitive data.
- Consumers can ask for copies of their data and evidence for how it’s being used.
HIPAA
Anyone working in healthcare (or anyone who’s been to a doctor’s office), is likely familiar with the healthcare data privacy act called HIPAA.
HIPAA requires providers to have appropriate safeguards in place to protect personal health information and sets limits on who can access it without the patient’s consent. In short, HIPAA ensures that personal health information is kept private and secure.
But in an industry with such heavy legal documentation requirements, remaining compliant is no easy feat.
With state-of-the-art security features, contract management software helps healthcare professionals navigate the choppy waters of HIPAA compliance. Not to mention, it streamlines the lengthy process of sharing documentation across care facilities.
Learn more about how contract management software can help healthcare professionals increase contract accessibility while remaining compliant.
CCPA
Established in 2018, the CCPA is sort of like California’s answer to the GDPR. This set of privacy laws and regulations requires businesses to give California citizens more control over the private information they share. Under the CCPA, California consumers have the right to:
- Know what personal information a business has collected about them and how it’s being used
- Delete any personal information collected from them
- Opt out of the sale or sharing of their private information
- Non-discrimination for exercising these rights
In 2020, California voters approved to amend the CCPA and added new privacy protections. As of January 2023, California consumers also:
- Have the right to correct personal information a business has processed about them
- Have the right to limit the use and disclosure of sensitive personal information collected
These rights can be applied to any for-profit business that targets California consumers and meet any of the following:
- Have a gross revenue of over $25 million
- Buy, receive, or sell personal data of at least 100,000 California residents or devices
- Derive at least half of its annual revenue from selling California residents’ personal information
If you’re not operating in California, your state likely has its own set of privacy laws to abide by. States like New York, Nevada, and Virginia have recently passed similar regulations to protect precious consumer data from hackers and annoying spam callers.
Other Laws To Keep an Eye On
In an age where consumers are sharing more personal information than ever before, the implementation of new ironclad privacy laws is on the horizon. While they may differ by location, platform, and industry, the main objective of all the latest regulations is largely the same — to protect consumer information and give consumers the right to decide how it’s used.
- Controlling the Assault of Non-Solicited Pornography and Marketing Act (CAN-SPAM): establishes the requirements for commercial emails and electronic mail messages and gives recipients the right to opt out or unsubscribe
- Gramm-Leach-Bliley Act (GLBA): requires financial institutions to disclose their data-sharing practices and safeguard private customer information
- Children’s Online Privacy Protection Act (COPPA): protects the personal information and online privacy of those age 12 and younger
- Apple App-Tracking Transparency Feature: allows consumers to choose whether an app can track their activity across other apps and websites for the purpose of advertising or sharing with data brokers
- Safari Third-Party Cookie Blocking: blocks all third-party cookies, preventing advertisers or websites from using cookies for cross-site resources
How Do Data Privacy Laws Impact Contract Management?
These privacy laws aren’t messing around. Companies need to make sure their contracts are written, stored, and managed with security rules and regulations at the forefront. Otherwise, you’re risking the faith your customers have in your organization (and the relationship with your lawyer, who will surely appreciate you following these laws as well).
Companies are not only obligated but are required to collect, store, and share personal information with integrity and care.
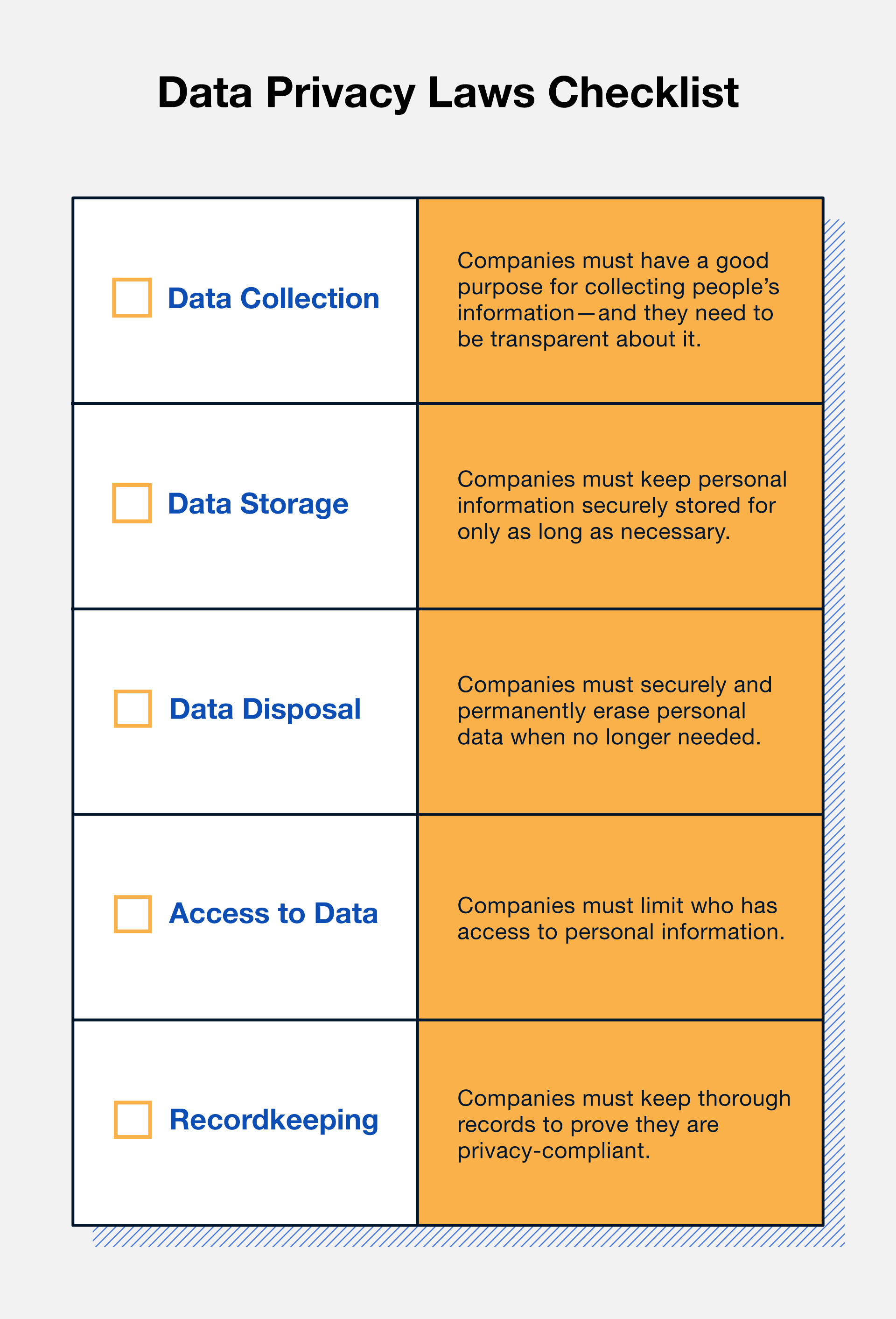
Data Collection
Companies must have a good reason for asking for personal information, and they need to let customers know why they need it and who will have access. Not to mention, they need to share how they’ll handle it, too.
In every set of privacy laws, there’s a clause concerning data collection purpose, transparency, and consent that outlines data collection best practices.
While these regulations seem fairly straightforward, there have been some challenges — take TikTok, for example.
In January 2023, the popular video-sharing platform was fined $15.9 million for allegedly misusing the data of children under the age of 13 (who aren’t supposed to be on the app, mind you). The U.K.’s Information Commissioner’s Office claimed TikTok did not take enough action to ensure underage users weren’t using the platform, and used their personal data without parental consent. Tsk tsk.
U.S. companies will soon find themselves jumping over complex hurdles with every new wave of regulations, especially when juggling federal and state-by-state cases.
Unlike the EU, the United States doesn’t have a standardized set of privacy laws (yet), so organizations need to maintain compliance with every applicable privacy rule. That requires
- Extensive, accessible intelligence regarding the state in which each U.S.-based customer resides
- Knowledge about the laws in effect in that jurisdiction
- The practical steps that the organization needs to take to comply with all of those separate regulatory standards
Data Storage
Once personal data has been collected and processed, it’s up to the data collector to keep it safe. From malware to password guessing, there are plenty of bad people who would love to get their hands on customers’ Social Security numbers or bank login information.
In fact, one of the largest data leaks in the U.S. occurred because of poor website security data measures. Approximately 885 million files containing bank account numbers, driver’s license numbers, and more were leaked from First American Financial Corp — an incident that could have been avoided with simple password-protected website links.
Organizations can take extra precautions when handling and storing contracts containing personal data by
- Keeping an inventory of all equipment such as computers, laptops, mobile devices, disks, drives, and home computers that may be used to access or store sensitive data
- Locking away physical documents, like paper files, thumb drives, and backups
- Requiring employees to lock files away and log off their computers when leaving their desks
- Encrypting personal information sent to third parties over public networks, stored on shared work networks or laptops, and emails sent within your business (maybe just encrypt everything, just in case)
- Implementing two-step authentication to access online accounts
- Using Transport Layer Security (TLS) encryption when transmitting financial data
Data Disposal
Most people throw their gum wrappers away instead of letting them pile up on their desk, right? The same practice can be applied to contract management.
If companies are in possession of defunct account information or loan applications of decades past, they need to get rid of this personal data if they no longer need it. A good way to keep track of aging contracts is by establishing and maintaining a records retention schedule to identify which documents are no longer necessary to keep.
However, it may take more than just hitting “delete” on your computer. Much like a pesky email spammer that you swear you unsubscribed from, the second component to data disposal is ensuring that data is really gone.
Organizations handling personal information should have a validated destruction process that aligns with the company’s records and information management (RIM) policy. You can also outsource your record retention, storage, and destruction to a third-party specialist.
|
Did you know? ContractSafe lets you set reminders for when it’s time to spruce up your spreadsheets and files. Check out our handy alert and reminders feature to help you stay on top of data disposal requirements. |
Access to Data
There’s no reason Kelly in marketing needs the HR records of all employees. Limiting which team members have access to sensitive personal information is an essential contract management best practice.
Access controls mitigate the risk of personal information being accessed without authorization. To ensure you’re following proper privacy compliance, only allow access to personal information to team members who need it to perform their roles.
Recordkeeping
So you’ve crossed your t’s and dotted your i’s on a hacker-proof, privacy-compliant data management process — now you have to prove you’re actually using it. Businesses need to keep accurate records of their information-processing activities and be able to provide evidence of compliance to auditors and regulators. This includes:
- Maintaining records of data subject requests
- Data protection impact assessments
- Data breach notifications
Keeping track of your company’s, employees’, and customers’ private information can quickly get out of hand, especially if you’re a large multi-unit business relying on antiquated data management systems. Luckily, technology has caught up to the demands of new data privacy compliance laws.
How Contract Management Software Ensures Privacy Compliance
If all that sounds like a handful, that’s because it is. Privacy compliance takes time — not to mention, it’s prone to tons of human errors.
That’s where we come in.
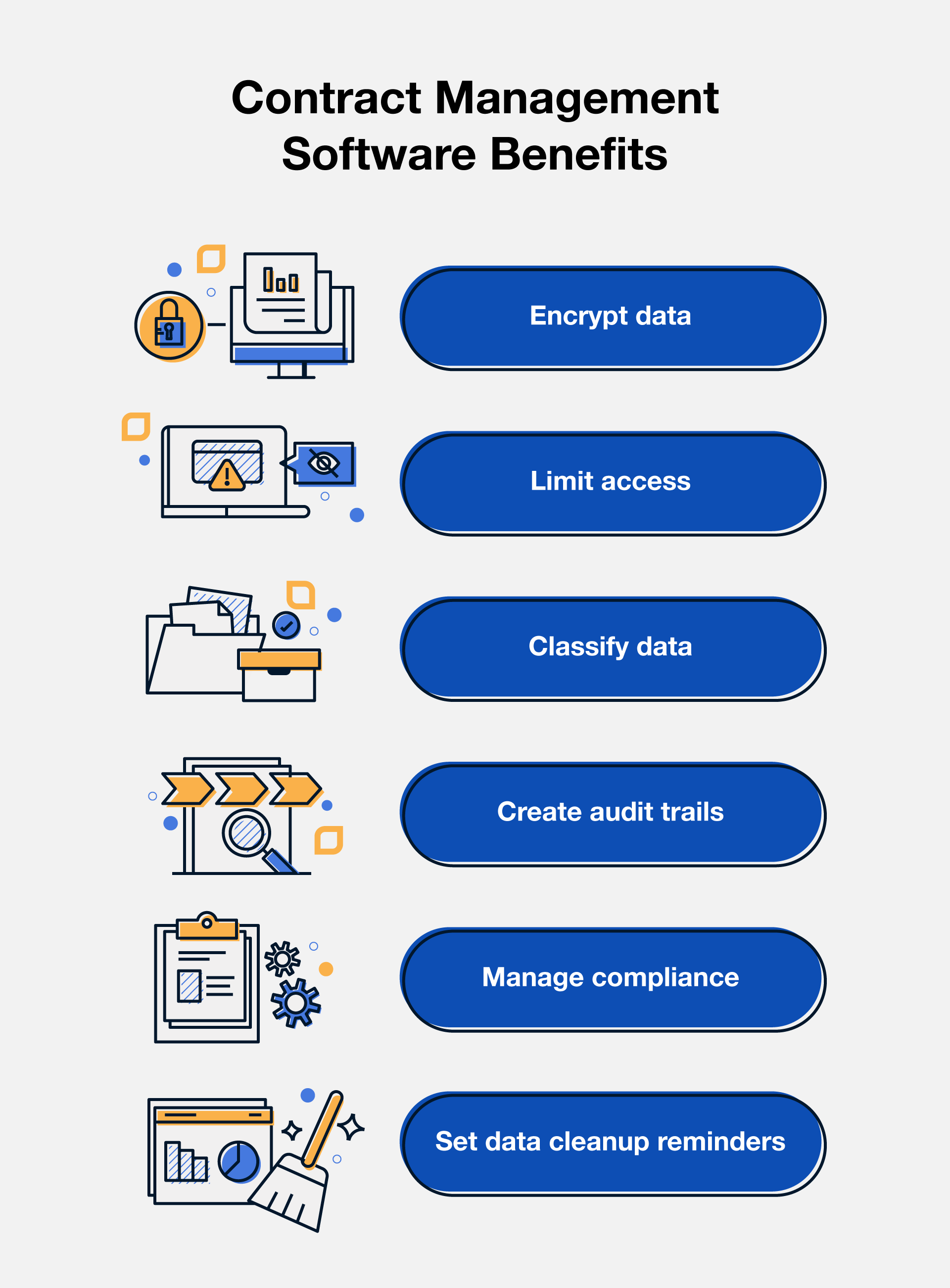
Contract management software like ContractSafe can help businesses overcome privacy compliance challenges in a variety of ways.
Utilize End-to-End Encryption for Better Security
Contract management software uses end-to-end encryption to protect contracts containing sensitive data in transit and at rest.
Encryption ensures the data is secure and protected from unauthorized access or disclosure. It’s just one of many contract management security features that can be used to protect data both inside and outside the system, including email communication, file transfers, and data storage.
Improve Visibility Into Contracts With Audit Trails and Reporting
Make sure you have all your ducks in a row the next time a compliance officer drops by your office. Contract management software helps make audits quicker and easier for everyone by
- Automatically logging user activity in real time with full audit trails to provide a comprehensive record of all data access and modification
- Generating reports that provide insight into data usage, user activity, and compliance with privacy laws
Make Contracts Easily Searchable With Data Classification and Customizable Permissions
Not sure how to keep Kelly from poking around in those sales forms? ContractSafe offers data classification and customizable user-level permissions for unlimited users to ensure everyone has access to exactly what they need — and nothing more.
This helps enforce policies related to user permissions, data retention, data subject rights, and data protection impact assessments. You can rest assured your contracts are organized and easily accessible only to the people who need them.
Take the Legwork Out of Compliance With Compliance Management
Some of the largest companies in the world will tell you privacy compliance is a major contract management challenge.
Compliance management involves implementing policies, creating procedures, and using controls to ensure businesses comply with applicable data privacy laws and regulations.
Contract management software can help businesses manage privacy compliance by providing tools to automate compliance workflows, track compliance activities, and generate compliance reports. New laws and revisions may require companies to update their MSAs or DPAs, but having compliance features already built into your CMS will make amendments much easier.
ContractSafe Makes Privacy Compliance Easy
We’re at a turning point in privacy compliance, and regulations will only become stricter as new security concerns arise. Future-proof your business by adopting an easy-to-use contract management software like ContractSafe to keep your contract processes in compliance. Schedule your demo today to discover how ContractSafe can help your business stay on top of privacy compliance.