Most contract headaches aren’t caused by bad intent or slow reviewers. They usually come from fuzzy handoffs, missing context, and approval rules that change depending on who’s in the thread. This guide lays out how Finance, Legal, and IT teams run contract intake, approvals, and execution in 2026 so decisions don’t stall.
- Good contract intake prevents rework. Capture purpose, owner, value, risk flags, and documents before review starts.
- Approval rules should be written down and leadership-backed so routing and review can happen in parallel.
- Lifecycle visibility keeps contracts from stalling mid-process by showing the stage, owner, and next action at all times.
If you’ve ever had to ask, “Where is this contract right now?” you already know the problem.
Somewhere between a forwarded PDF, a “quick question” from Finance, and an IT security review that shows up late to the party, contracts can drift into the Bermuda Triangle. Nobody’s trying to be difficult. Teams just don’t share the same assumptions about how the contract intake, approval, and execution process is supposed to work.
Most delays don’t come from the review itself. They come from everything around it: unclear intake, undocumented approval expectations, and handoffs that happen in the dark.
And each team feels that breakdown differently. Finance sees budget exposure. Legal sees risk creep. IT sees security gaps introduced too late in the process.
What is an end-to-end contract workflow?
An end-to-end contract workflow is the complete process a contract follows from initial request through signature, obligation tracking, and renewal. It connects every handoff - intake, review, approval, execution, and post-signature management - into one visible path instead of a patchwork of emails and spreadsheets.
Why End-to-End Contract Workflows Break Down Across Teams
Contract workflow breakdowns usually start before review begins. Intake gaps, undocumented approval expectations, and informal routing create invisible delays that compound as contracts move across teams. Understanding where workflows fail makes it easier to design processes that prevent rework and stalled decisions.
It’s tempting to blame contract delays on Legal being swamped. In reality, the mess usually starts before Legal is even meaningfully involved.
Here’s what tends to break first:
-
Intake shows up incomplete. Reviewers end up chasing basics midstream: scope, pricing, timeline, what’s attached, who owns it. Intake often arrives through email, Slack, or forwarded documents with missing context.
-
Approval expectations are inconsistent. The “right” approver changes based on who’s available or who handled the last one. Routing is based on habit, not written rules.
-
Routing happens informally. “Loop in Finance just in case” becomes the default, which adds noise and slows down real decisions.
-
Execution gets treated like “the end,” so post-signature tracking becomes an afterthought.
-
Nobody has shared visibility. Teams don’t know what stage the contract is in, who owns the next move, or what it’s waiting on until someone escalates.
Research from World Commerce & Contracting shows that organizations lose an average of 9.2% of contract value when post-signature management is weak. That loss doesn’t come from slow legal review, but from unclear ownership, missed obligations, and poor lifecycle visibility.
Before we talk fixes, here’s the simple model to keep in your head:
 (Lifecycle tracking runs across every stage)
(Lifecycle tracking runs across every stage)
That’s what “healthy” looks like. Everything else in this article maps back to it.
RELATED READ: How To Simplify Your Contract Workflow With Contract Management Software
Designing Contract Intake That Prevents Rework Later
Effective contract intake prevents rework by capturing the contract’s purpose, owner, value, risk indicators, and all related documents before review begins.
Strong intake helps each team start with clarity:
-
Finance: Flags unusual spend, renewal structure, and budget exposure early
-
Legal: Identifies nonstandard terms before negotiation begins
-
IT/Security: Spots data access, integration, or security review needs upfront
When intake is weak, reviewers spend their time doing detective work. When intake is solid, reviewers can focus on decisions.
What good intake accomplishes
Good intake does a few important things right away:
-
Sets the why. What’s the business purpose, and what are we trying to accomplish?
-
Sets the who. Who owns this relationship and will answer questions without disappearing?
-
Sets the size. Rough value, payment structure, and what counts as “nonstandard” for your org.
-
Sets the risk flags. Data access, system integrations, security requirements, regulated terms, and renewal exposure.
That’s not busywork. It prevents the same questions from popping up three times in three different inboxes.
What to capture upfront (and what not to)
You don’t need a 50-field intake form. You need a handful of details that stop rework later.
Capture up front:
-
Contract purpose and counterparty
-
Estimated value and payment structure
-
Timing expectations (is there a real deadline or just a loose target?)
-
Data/system access indicators for IT/security review
-
All relevant documents at submission (main agreement, SOWs, exhibits, amendments)
And one big rule: every request needs a named owner. If the contract has no owner, it becomes everybody’s problem, which means it becomes nobody’s priority.
Payoff: Standardized intake doesn’t “speed up Legal.” It removes ambiguity before the review even starts, which cuts down the back-and-forth that makes everything feel slow.
Designing a Contract Approval Process That Actually Scales
Approval problems rarely come from “too much process.” They come from trying to make decisions without agreeing, in writing, on what the decisions are.
If your workflow keeps getting stuck at approvals, it usually means the organization hasn’t nailed down its approval rules.
Here’s what scalable approvals have in common:
-
Approval rules live in a written policy that leadership agrees to
-
Routing reflects that policy instead of reinventing it contract-by-contract
-
Escalation triggers are based on risk and exposure, not whoever happens to be on the email thread
A few examples of what tends to work:
-
Finance review triggers tied to multi-year commitments, auto-renewals, nonstandard payment terms, and spend exposure
-
Legal escalation tied to changes in risk posture (liability caps, indemnity scope, audit rights, governing law)
-
IT/security review required when vendors touch systems or sensitive data
The workflow doesn’t need to “be smart.” It needs to follow the rules your organization has already decided are smart.
RELATED READ: How To Scale Your Contract Management Processes: Key Considerations for Small Businesses
How Cross-Functional Contract Review Actually Works in Practice
“Review” is often treated like one step. In reality, it’s multiple reviews happening for different reasons.
Finance, Legal, and IT aren’t looking for the same things:
-
Finance is checking spend exposure, payment terms, budget impact, and renewal commitments.
-
Legal is checking enforceability, liability exposure, regulatory obligations, and clause consistency.
-
IT/Security is checking data access, integration requirements, security controls, vendor SOC 2 posture, and operational risk tied to systems and infrastructure.
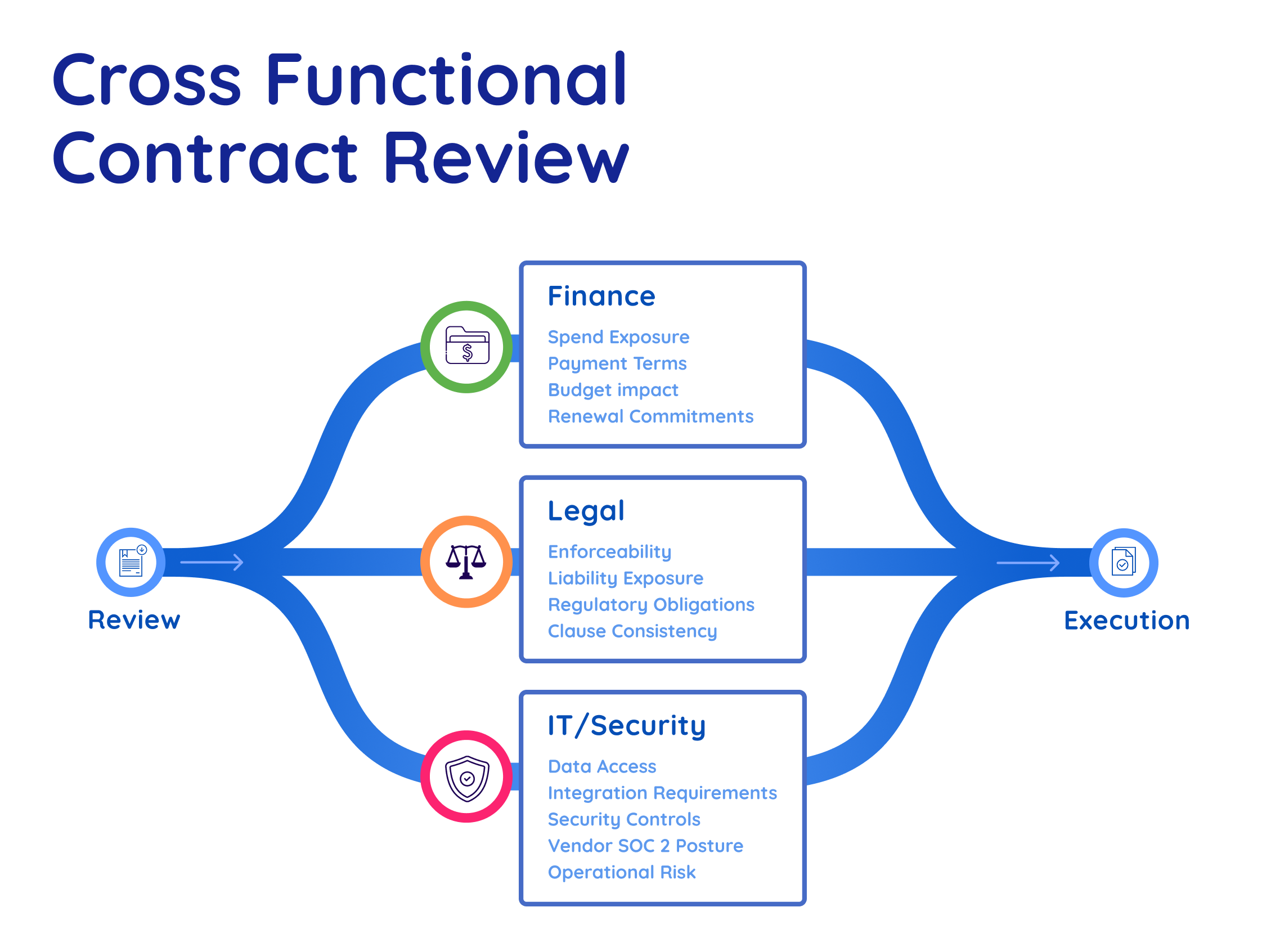
Each team’s review affects timing differently. Budget exposure can pause Finance approval, risk allocation can pause Legal, and security or integration concerns can pause IT.
Delays happen when those roles blur or pile on top of each other. In practice, cross-functional review works best when routing rules clearly define whether teams review in parallel or sequence, with clear ownership and documented outcomes.
✅ What Finance Is Evaluating
Finance isn’t just checking the price. They’re evaluating how a contract affects the organization’s financial position and whether the terms create exposure that isn’t visible at first glance.
Key areas Finance reviews:
-
Budget alignment and forecast impact. Does this contract fit within approved spend, or does it require additional budget approval? How does it affect quarterly or annual forecasts?
-
Revenue recognition implications. For customer-facing contracts, how and when revenue gets recognized matters for reporting accuracy and compliance
-
Multi-year commitment and exit costs. What’s the total exposure over the life of the agreement? What happens if priorities shift and you need to exit early?
-
Auto-renewal terms and cancellation windows. Contracts that auto-renew without notice create silent budget commitments. Finance needs to know when cancellation windows open and what notice is required.
-
Payment terms and cash flow impact. Net 90, milestone-based payments, prepayment requirements, and late-payment penalties all affect cash flow planning. Terms that look standard on paper can create real operational pressure.
Finance review ensures the organization doesn’t quietly overcommit to terms that create budget pressure down the road.
✅ What Legal Is Evaluating
Legal review goes well beyond whether the contract "looks okay." Legal is assessing whether the terms are enforceable, whether they create disproportionate risk, and whether the organization can actually live with what's being agreed to.
Key areas Legal reviews:
-
Liability caps and indemnification scope. Who's on the hook if something goes wrong, and is the exposure proportionate to the deal value? Uncapped or one-sided indemnification is one of the most common red flags.
-
IP ownership and licensing terms. Who owns work product created under the contract? Are licensing rights clear, and do they survive termination?
-
Termination rights and cure periods. Can either party exit, and under what conditions? Are cure periods reasonable, or do they lock you into a bad situation?
-
Governing law and dispute resolution. Where would a dispute be heard, and under what rules? This matters more than most people realize until it matters a lot.
-
Regulatory and compliance obligations. Does the contract create obligations under data privacy laws, industry regulations, or internal compliance policies? Are those obligations clearly assigned?
-
Non-compete and exclusivity clauses. Do any terms restrict the organization's ability to work with other vendors or operate in certain markets?
The goal isn’t a perfect contract. It’s a risk that’s understood, proportionate, and documented.
✅ What IT & Security Are Evaluating
IT and security review is about understanding the operational risk a contract introduces to your systems, data, and infrastructure. When IT gets pulled in late, the most common result is a last-minute scramble over security requirements that should have been addressed from the start.
Key areas IT/Security reviews:
-
Data classification and handling requirements. What types of data will the vendor access, process, or store? Is it PII, financial data, health records, or other sensitive categories? How the vendor handles that data needs to match your internal policies.
-
Vendor security posture. Does the vendor hold relevant certifications like SOC 2, ISO 27001, or HITRUST? Has a vendor security assessment been completed, and are the results acceptable?
-
System access and integration scope. Will the vendor need access to internal systems, APIs, or infrastructure? What's the scope of that access, and how is it controlled and monitored?
-
Data residency and storage. Where will data be stored and processed? For organizations with regulatory requirements or internal policies around data residency, this can be a dealbreaker if missed.
-
Incident response and breach notification. What happens if there's a security incident? Are notification timelines and responsibilities clearly defined in the contract?
-
Compliance with security policies and regulations. Does the contract meet requirements under frameworks like GDPR, HIPAA, CCPA, or your organization's internal security standards?
This is the checkpoint that prevents a signed contract from becoming a security incident.
✅ What helps contract reviews move without getting sloppy
A few things make a big difference:
-
Parallel review when appropriate. For standard agreements with clear intake and defined routing rules, teams can review at the same time instead of waiting in line. For high-risk or highly negotiated contracts, sequencing reviews may be more effective, so one team’s findings can inform the next.
-
Clear outcomes. “Approved,” “approved with exception,” or “rejected” beats “looks fine” every day of the week.
-
Version visibility. Approvals only mean something if everyone knows what changed between drafts.
When the responsibilities are clear, review stops feeling like a relay race where the baton keeps getting dropped.
Where Contract Approvals Still Get Stuck, and How Teams Fix It
Even with intake forms and approval rules, contracts still stall. That’s normal. It’s also fixable.
Most stalls come from:
-
No clearly assigned owner at the current stage
-
No defined next action or decision required
So the contract just… waits.
What fixes bottlenecks in the real world
Teams that reduce stalls consistently do a few boring-but-effective things:
-
Define who owns each stage (not just “Legal owns it”)
-
Make status visible: stage, owner, and what the contract is waiting on
-
Agree on a time-in-stage threshold for “stalled” so delays get flagged early
-
Use reminders to reinforce ownership, not replace it
If you can see where work is piling up, you can actually do something about it. If you can’t, you’re stuck with guesswork and escalation.
How Clear Intake and Approvals Shape Contract Execution
Contract execution becomes predictable when intake is complete, and approvals are documented before signature. Execution is the part everyone wants to “just happen.” And it usually does… when the upstream work is done.
When intake is solid and approvals are documented, signature becomes a predictable step instead of a late-night scramble.
A few realities worth calling out:
-
eSignature helps a lot, but it can’t rescue unclear approvals or missing context
-
Execution goes smoother when everyone can see that approvals are complete and exceptions are documented
-
Teams should confirm execution is complete before shifting into post-signature tracking
This section isn’t about long-term compliance reporting. It’s about confidence at the finish line: you know what’s signed, by whom, and that it’s actually final.
RELATED READ: How Contract Management Software Streamlines Processes
How Contract Lifecycle Visibility Ties Intake, Approval, and Execution Together
Contract Lifecycle visibility ties the process together by showing where a contract is, who owns it, and what it’s waiting on at every stage.
This kind of visibility isn’t micromanagement. It’s the shared understanding that keeps cross-functional work.
In regulated environments, especially, visibility is what lets you answer basic questions without panic:
-
Where is this contract right now?
-
Who owns the next step?
-
What happens next?
What “good visibility” shows
Lifecycle visibility works when it provides:
-
Clear lifecycle stages with a shared meaning
-
Ownership per stage
-
What the contract is waiting on
-
A record of how decisions were made (not just what was signed)
That last point matters. If you ever need to explain how a decision happened, “we think it was approved in a thread somewhere” is not the vibe.
RELATED READ: Contract Lifecycle Tracking: Why Visibility Matters Across Every Stage
How ContractSafe Supports End-to-End Contract Workflows Without Replacing Judgment
This is where tools should help, not hijack the process.
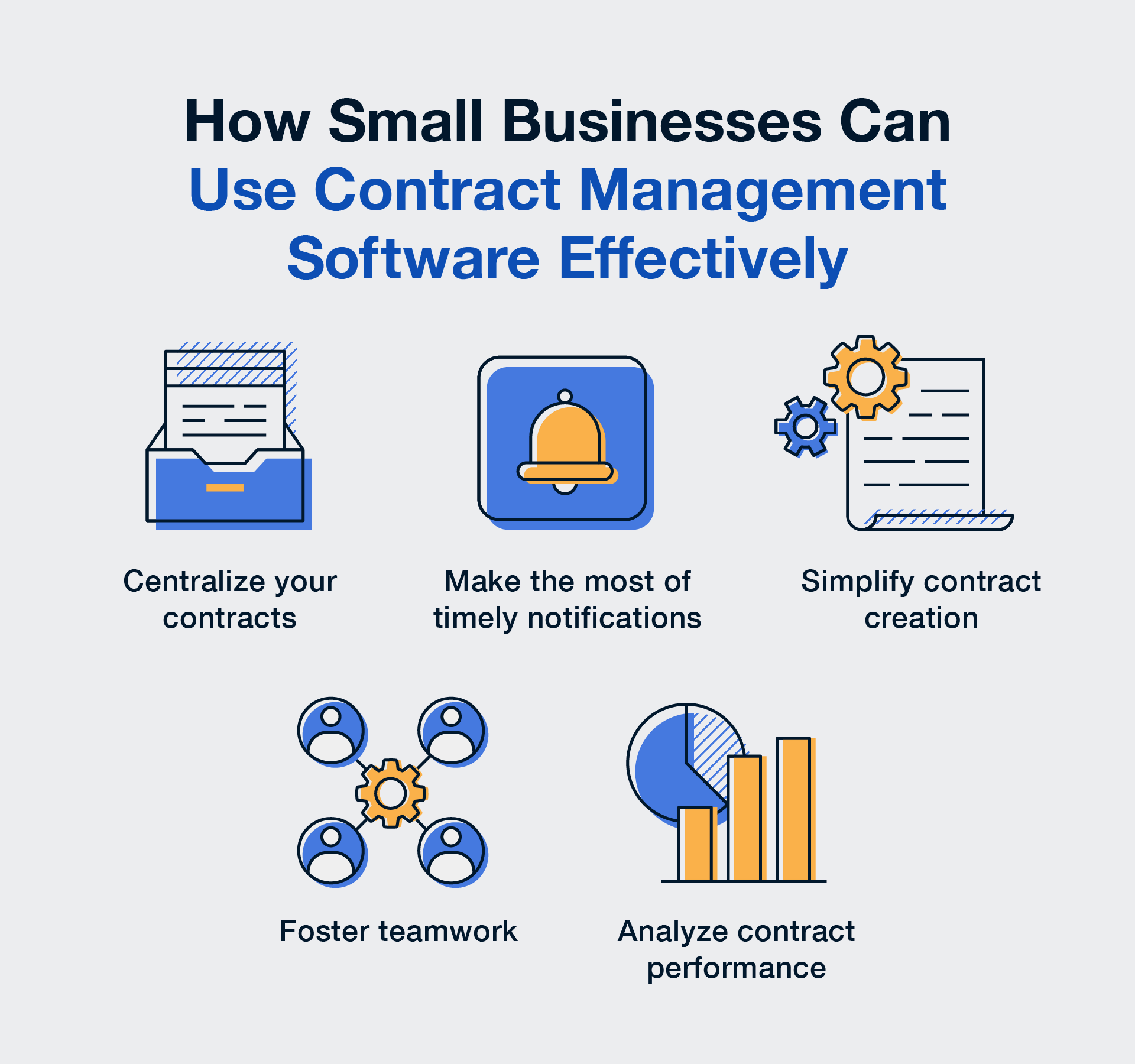
ContractSafe can support an end-to-end contract workflow by giving teams one place to manage the mechanics:
-
Central system of record for contracts and related documents
-
Structured intake so requests come in with the right context and attachments
-
Approval workflows that route contracts to the right people without endless email chains
-
Integrated e-signature so execution doesn’t mean switching to another platform
-
Role-based access so you can control who sees, edits, and manages contracts across teams like Finance, Legal, and IT
-
Lifecycle tracking so teams can see which stage a contract is in, who owns it, and what it’s waiting on
-
Activity history that supports auditability and defensibility
And the important boundary: ContractSafe doesn’t decide whether you accept risk, escalate, or approve an exception. That stays with your policy and your people.
Bringing Clarity to End-to-End Contract Workflows
The teams that run contracts well don’t rely on luck, memory, or heroic follow-ups. They build a workflow that holds up under pressure:
-
Intake comes in with enough context to review once
-
Approval rules are written down and leadership-backed
-
Review happens with clear roles and outcomes
-
Execution is confirmed and finalized cleanly
-
Lifecycle tracking keeps the work visible after signature
That’s what end-to-end contract workflows look like when they’re working.
ContractSafe supports the structure and lifecycle visibility that keep contracts moving across Finance, Legal, and IT.
If you want to see what that looks like in your environment, schedule a demo and walk through your workflow end-to-end.
Key Takeaways
-
Contract workflows usually break upstream. Missing intake details and undocumented approval expectations cause most downstream churn.
-
Approval rules scale when they’re written and leadership-approved, not implied through precedent.
-
Automation is best used for repeatable workflow steps like routing, reminders, and execution tracking. Judgment calls still belong to people and policy.
-
Lifecycle visibility reduces stalls by showing stage, owner, and next action while contracts are moving, not weeks later.
FAQs
How should contracts be routed for approval across Finance, Legal, and IT?
Routing should follow a written approval policy. Finance, Legal, and IT review different risks, so routing rules should spell out when each group is required based on factors like contract value, payment structure, risk exposure, data access, and system integration.
What parts of the contract process can be automated?
The best candidates for automation are repeatable, rules-based steps: intake submission, document routing based on pre-defined criteria, approval workflows, and execution tracking. These steps benefit from consistency and speed.
What contract decisions shouldn't be automated?
Decisions involving financial exposure, legal risk, exception handling, and risk acceptance should stay with people and policy. Software can document and enforce the rules, but it shouldn't be making the calls.
How do teams prevent contracts from stalling during review or approval?
Assign an owner at each stage, make status visible (including what the contract is waiting on), and define a “stalled” threshold based on time in stage. That combination surfaces issues early, before deadlines get tight.
How does contract lifecycle visibility support compliance and audits?
Contract Lifecycle visibility provides a traceable record of how a contract moved from intake through review, approval, and execution. It helps teams show who reviewed, who approved, when decisions were made, and how exceptions were handled.
What role should contract management software play in an end-to-end workflow?
Software should support structure, visibility, and documentation across the contract lifecycle, while leaving risk decisions to policy and people. The goal is consistent processes and audit-ready records without replacing judgment.
Which is better: a contract repository or a CLM?
Neither is universally “better.” A contract repository is ideal for post-signature organization and audit readiness. A CLM is better suited for teams that need structured workflows across intake, drafting, approvals, and negotiation. The right choice depends on how complex your contract processes have become.
What approval decisions should remain human-owned?
Approval decisions tied to financial exposure, legal risk, exception handling, and risk acceptance should remain human-owned. Software can document and reinforce policy, but organizations must define and own risk decisions.
What’s the difference between contract workflow visibility and contract storage?
Contract workflow visibility shows where a contract is in the lifecycle, who owns it, and what decisions are pending. Contract storage only preserves the document after execution. Visibility supports coordination, while storage supports recordkeeping.