CIRCIA compliance is often framed as a cybersecurity or IT challenge. In reality, many organizations will fall out of compliance for a simpler reason: their vendor contracts don’t require timely incident reporting, cooperation, or accountability when something goes wrong. As the Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) moves toward its final rule, legal teams are being pulled into the center of incident response readiness. Most CIRCIA compliance failures won’t happen because incidents weren’t detected, but because organizations couldn’t legally compel vendors to respond fast enough.
CIRCIA reporting deadlines can start before you hear a word from your vendors. That timing gap—not detection failures—is where most organizations will fall out of compliance. If your contracts don’t require vendors to report suspected incidents immediately and share usable details fast, your legal reporting clock may already be running without you knowing it. Fixing contract language now is the only way to control that risk.
What CIRCIA Requires and Why Contracts Are the Weak Point
At its heart, the Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) is about speed and transparency. It requires organizations in critical sectors, including healthcare, energy, and parts of the financial services ecosystem, to report substantial cyber incidents to the Cybersecurity and Infrastructure Security Agency (CISA) within 72 hours.
If a ransom payment is made in response to a ransomware attack, a separate report must be submitted within 24 hours of payment. These timelines often overlap, which makes delayed vendor notification especially risky.
CISA has indicated May 2026 as its current target for finalizing the rule, but timelines can still shift. Regardless of the exact date, vendor contracts don’t change quickly, and waiting guarantees you’ll be behind when enforcement begins.
Most modern businesses rely on a web of third-party vendors to handle data, hosting, and operations. If a vendor experiences a cyber incident but waits five days to tell you, your 72-hour reporting clock has already expired before you even knew it started. This makes your vendor contracts the single biggest weak point in your compliance strategy.
CIRCIA’s Reporting Timelines Depend on Third-Party Information
The CIRCIA reporting clock does not wait for a vendor to complete its internal investigation or confirm root cause. It starts as soon as a covered entity—an organization operating in a CIRCIA-designated critical infrastructure sector such as healthcare, energy, transportation, or certain financial services—reasonably believes an incident occurred.
Because so many incidents originate within service provider environments, your visibility is naturally delayed. Without a contract that forces a vendor to speak up early, you are left in the dark. You can’t compel a vendor to cooperate because it’s the right thing to do. You need clear, contractual obligations that require them to disclose suspected issues immediately so you can meet your legal filing requirements.
In practice, this creates a timing mismatch. Vendors often prioritize containment and internal investigation before notifying customers. While that may make sense for their own response, it works directly against CIRCIA’s reporting deadlines. If a contract only requires notice after confirmation, the vendor may wait days or weeks, long after your reporting window has already started.
Why IT Controls Alone Can’t Ensure CIRCIA Compliance
Your IT team might have the best security tools on the market, but those tools stop at your digital front door. Security software can detect a breach on your server, but it can't tell you what is happening on a vendor's server, force a vendor to tell you why their system is down, or spell out what data was lost.
The legal responsibility for reporting rests with you, the covered entity, regardless of where the incident happened. Contracts act as the enforcement bridge. They take the technical reality of a third-party breach and turn it into a legal obligation for that vendor to provide the facts you need to stay compliant.
RELATED READ: The Ultimate Contract Repository Guide: How to Build, Automate, and Prove ROI
Why Vendor Delays Make You Non-Compliant
In the world of cyber incidents, there is a natural tension: vendors want to be 100% sure of the facts before they report an initial red flag, while regulators want you to report as soon as you have a "hunch." This mismatch creates a compliance gap that can lead to enforcement risk and audit exposure.
Missing Contract Language Leaves No Way to Enforce Timelines
If your contract says a vendor will notify you of a breach in a commercially reasonable timeframe, you’ve already lost. “Reasonable" is a lawyer's favorite word because it’s vague. Without explicit notice windows (for example, 12 hours from discovery), you have no leverage to accelerate vendor response or demonstrate good-faith compliance during a regulatory review. In a crisis, vague language doesn’t just slow you down—it leaves you exposed.
You’ll find yourself in an ad-hoc negotiation during the middle of a cyber crisis, which is the worst possible time to be arguing over what counts as an incident.
RELATED READ: Contract Lifecycle Management - 12 Common Questions Answered
The 4 Contract Clauses You Must Renegotiate Before May 2026
To get ready, you don't need to rewrite every page of your agreements, but you do need to sharpen these four specific areas. Think of these as your incident response toolkit.
1. Incident Notification Timelines and Triggers
Notification clauses must be precise because ambiguity is the primary cause of delay. If your trigger is a confirmed breach, you’ve already missed the CIRCIA window.
-
Update the Trigger: Change triggers to include "suspected incidents" or "potential unauthorized access." Confirmation often comes days after the regulatory reporting requirement has already been triggered.
-
Set Concrete Deadlines: Replace "promptly" with specific windows (e.g., 12 or 24 hours). This allows you enough time to evaluate the vendor’s information and prepare your own filing to CISA.
-
Focus on Discovery: The clock should start at the vendor's discovery of the anomaly, ensuring that their internal investigation doesn't hide the incident from your view until it's too late.
2. Vendor Cooperation and Information-Sharing Obligations
CISA doesn't just want to know that you had an incident; they need specific details to help protect other organizations. This is where many contracts fall short, often because they contain overly broad confidentiality clauses.
-
Confidentiality Carve-outs: Ensure the vendor is explicitly permitted to share incident details with you and that you have the explicit right to share that information with CISA and other regulators without breaching your contract's confidentiality terms.
-
Detailed Reporting Requirements: Cooperation must include providing scope, impact, remediation steps, and root-cause details as they become available. An email saying “we had an incident” is not helpful unless your clause requires specific fields, such as:
-
-
Suspected incident type
-
Systems affected
-
Customer environments impacted
-
Initial containment steps
-
Data categories potentially involved
-
Whether law enforcement engaged
-
-
-
Ongoing Updates: Reporting isn't a "one and done" event. Require the vendor to provide continuous updates so you can meet CIRCIA’s supplemental reporting requirements as more facts emerge.
3. Audit Rights and Verification of Incident Response
You cannot support a credible regulatory review based solely on an assumption or a vendor’s verbal promises. You must be able to verify what happened to ensure your reporting is accurate and defensible.
-
Targeted Audit Rights: While vendors often push back on open-ended walk-through data center audit rights, you should insist on the right to obtain incident artifacts, timelines, and post-incident root cause summaries.
-
Cost Allocation: Clearly define who pays for incident support. This includes forensic cooperation, rush reporting support, and third-party investigation costs. If this isn't settled in the contract, it will become a fight during the incident, further delaying your ability to report.
-
Independent Assurance: Require the vendor to provide current independent validation, such as SOC 2 reports or executive summaries of their most recent penetration tests, to prove their response capabilities are up to par.
4. Subcontractor and Supply Chain Flow-Down Requirements
Most cyber incidents today don't happen at the primary vendor level; they happen three or four layers deep in the supply chain. If your reporting obligations don't flow down, your visibility stops at the first contractual layer.
-
Mandatory Flow-Downs: Require your primary vendors to pass your reporting and cooperation timelines down to their own subcontractors.
-
Subprocessor Visibility: You need an operational mechanism for oversight. Include a requirement for a current subprocessor list and mandatory notice of any changes. If you don't know who is processing your data, you can't assess the risk when a new breach makes the headlines.

RELATED READ: How to Audit Your Contract Management Process
How CIRCIA Impacts Regulated and Adjacent Industries
CIRCIA’s practical impact is not uniform across the business landscape. It moves through the ecosystem, hitting some sectors with the force of a tidal wave while others feel a steady, inevitable pull toward higher standards. The intensity of the impact usually depends on two factors: the level of existing regulatory pressure and how much an organization depends on third-party digital systems to function. Because these reporting obligations cascade through supply chains, even organizations that don't consider themselves "critical infrastructure" may soon find that their customers, and their contracts, beg to differ.
Healthcare, Energy, Financial Services, and Transportation
For those in highly regulated sectors like financial services, healthcare, energy, and transportation, CIRCIA adds a significant layer of complexity to an already crowded regulatory landscape. These industries face heightened scrutiny because an incident doesn't just impact a balance sheet; it impacts public safety and systemic stability. The most intense reporting friction typically shows up in these environments because they face tight notification expectations and rely almost entirely on third parties to surface incident scope and remediation details. A single vendor incident can trigger a domino effect of overlapping obligations, where a legal team might find themselves trying to satisfy HIPAA, SEC, and CISA requirements all within the same 72-hour window.
When contract gaps exist in these industries, the exposure is compounded across multiple regulatory frameworks. To mitigate this, legal teams need "lifecycle-ready" contracts that do more than just mention security. Specifically, contracts must include explicit language ensuring that a vendor can share necessary details with you and that you have the right to pass that information to CISA or other regulators without breaching standard confidentiality clauses. It is also essential to settle the question of who pays before a crisis hits. Your agreements should clearly outline cost allocation for incident support, covering everything from forensic cooperation to rush reporting fees, so that a financial dispute doesn't stall your compliance filing while the clock is ticking.
SaaS and Vendors Serving Regulated Customers
Even if your company isn't directly classified as "critical infrastructure," you likely inherit these compliance expectations through your customer relationships. In the post-CIRCIA world, being a SaaS provider or a service vendor for a regulated entity means you are effectively a part of the critical infrastructure supply chain. Customers are increasingly viewing the ability to report incidents within a 24- or 72-hour window as a non-negotiable requirement for doing business. If your contract doesn't align with their regulatory needs, it creates a massive commercial risk that can lead to lost deals and damaged reputation.
However, there is a significant silver lining for proactive vendors. By updating contracts early to align with customer CIRCIA reporting expectations, you turn a compliance headache into a commercial differentiator. It shows customers that you understand their high-stakes environment and are prepared to support them when things go wrong. An essential part of this readiness is providing better operational visibility into your own supply chain. Beyond general flow-down clauses, you should offer customers a mechanism for subprocessor visibility, such as a live subprocessor list and a commitment to provide notice of any changes. By treating contract readiness as a partnership rather than a chore, vendors can improve customer trust and retention in an increasingly regulated market.
Despite the differences in how these industries operate, the common denominator remains the same: contract readiness is the only way to ensure that when a cyber incident occurs, you aren't left holding the bag for a reporting delay you couldn't control.
RELATED READ: Contract Lifecycle Management Process Best Practices: The Ultimate Guide
Preparing Contracts Now for the CIRCIA Final Rule
Positioning your organization for CIRCIA readiness is a sequencing exercise, not an overnight overhaul. Waiting for the ink to dry on the final rule text is a high-risk strategy; instead, legal teams should focus on prioritization and cross-functional alignment. By taking a structured approach now, you can reduce disruption and ensure that when enforcement begins in May 2026, your vendor ecosystem is already aligned with your reporting obligations.
For teams managing hundreds of vendor agreements, this kind of prioritization is difficult without centralized contract visibility and searchable clause data.
Prioritizing High-Risk Vendors and Agreements
Not all vendors pose an equal risk to your CIRCIA compliance. Trying to renegotiate every agreement in your repository simultaneously is a recipe for burnout and administrative gridlock. Instead, start by taking a targeted inventory of your vendor tiering.
Focus first on high-risk vendors, those with direct access to your internal systems, those who host sensitive customer data, or those providing mission-critical services that would trigger a 72-hour reporting window if they went offline. High-volume contracts also deserve early attention, as they represent the highest statistical likelihood of a missed obligation. By prioritizing these "keys to the kingdom" agreements, you can achieve the most significant risk reduction with the least amount of wasted effort, allowing you to move through the rest of your portfolio systematically.

Aligning Legal, Security, and Procurement Early
CIRCIA compliance is a team sport, and silos are the primary reason reporting windows are missed. To succeed, you must align the three pillars of vendor management: Legal, Security, and Procurement, well before an incident occurs.
-
Legal must define the enforceable reporting and cooperation language that bridges the gap between a vendor's internal investigation and your regulatory requirements.
-
Security teams are essential for identifying the actual technical dependencies. They know which vendors have "write" access to your databases or which SaaS tools are integrated into your core infrastructure.
-
Procurement acts as the enforcement arm, ensuring that updated CIRCIA clauses are baked into every new RFP and every upcoming renewal.
Early alignment ensures that these departments aren't meeting for the first time during a cyber crisis. By establishing a shared workflow now, you prevent emergency contract negotiations and ensure that your organization’s response is a well-oiled machine rather than a fire drill.
RELATED READ: How Contract Management Software Streamlines Processes
Preparing Vendor Contracts for CIRCIA Is a Legal Imperative
At the end of the day, CIRCIA compliance lives in your file cabinet (or your digital repository), not just your server room. Your technical controls can find a problem, but only your contracts can force a vendor to help you fix it and report it on time.
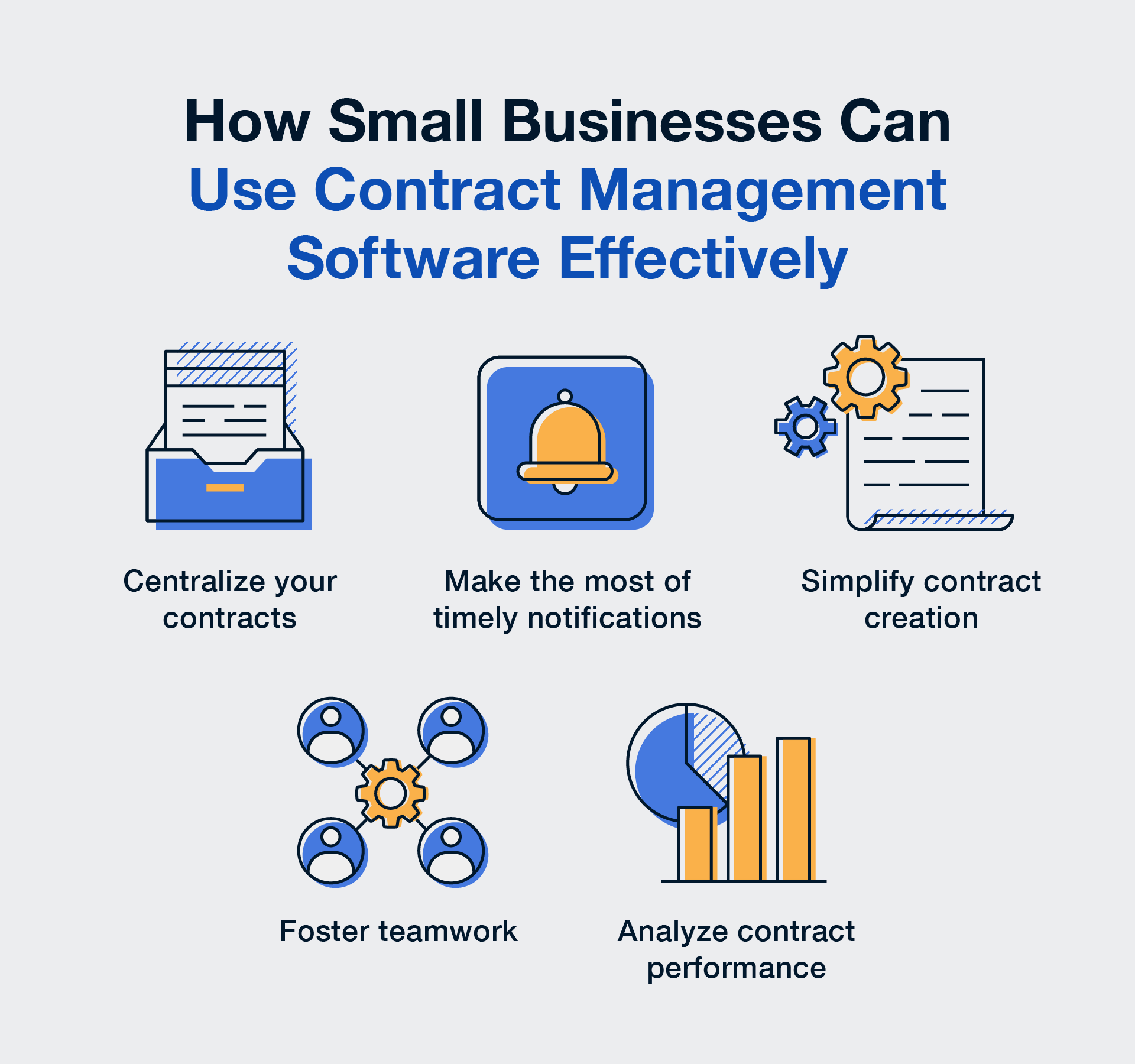
The challenge for legal teams isn’t just knowing what to change; it’s being able to find every vendor who needs a contract update. For teams managing hundreds of agreements, tools like ContractSafe make this easier by centralizing your vendor agreements and allowing legal teams to quickly identify contracts with weak notification, cooperation, or audit language.
In practice, this gives legal teams a clear, searchable view of vendor contracts that impact CIRCIA compliance. Teams can quickly identify agreements with vague or missing incident notification language, prioritize high-risk vendors for renegotiation, track which contracts require updates before renewal, and demonstrate good-faith compliance efforts during audits or regulatory inquiries. Instead of scrambling during a cyber incident, organizations know exactly which vendors are obligated to report, how quickly they must respond, and what information they are required to provide.
Don't wait for a regulator to ask for your reporting plan—get your contracts CIRCIA-ready today.
Key Takeaways
-
Cooperation is Mandatory: You cannot meet CIRCIA's 72-hour window without a contract that forces vendors to cooperate immediately.
-
Contracts are the Lever: Technical tools find breaches; contracts provide the legal leverage to get the information you need for CISA.
-
Focus on the "Big Four": Prioritize updating clauses for notification triggers, information-sharing, audit rights, and subcontractor flow-downs.
-
Expect a Cascade: If you serve regulated customers, expect them to push these obligations onto you as a condition of doing business.
-
Start Early: Renegotiating contracts takes time. Prioritize your high-risk vendors now to avoid a compliance crunch in 2026.
FAQs